Documentation Index
Fetch the complete documentation index at: https://www.qovery.com/docs/llms.txt
Use this file to discover all available pages before exploring further.
Overview
Cluster Advanced Settings allow you to fine-tune infrastructure-level parameters for your Qovery-managed Kubernetes clusters. These settings provide granular control over networking, logging, security, resource allocation, and cloud provider-specific features.Cloud Provider Availability
Settings are tagged with their supported cloud providers:AWS
Amazon Web Services
GCP
Google Cloud Platform
Azure
Microsoft Azure
Scaleway
Scaleway
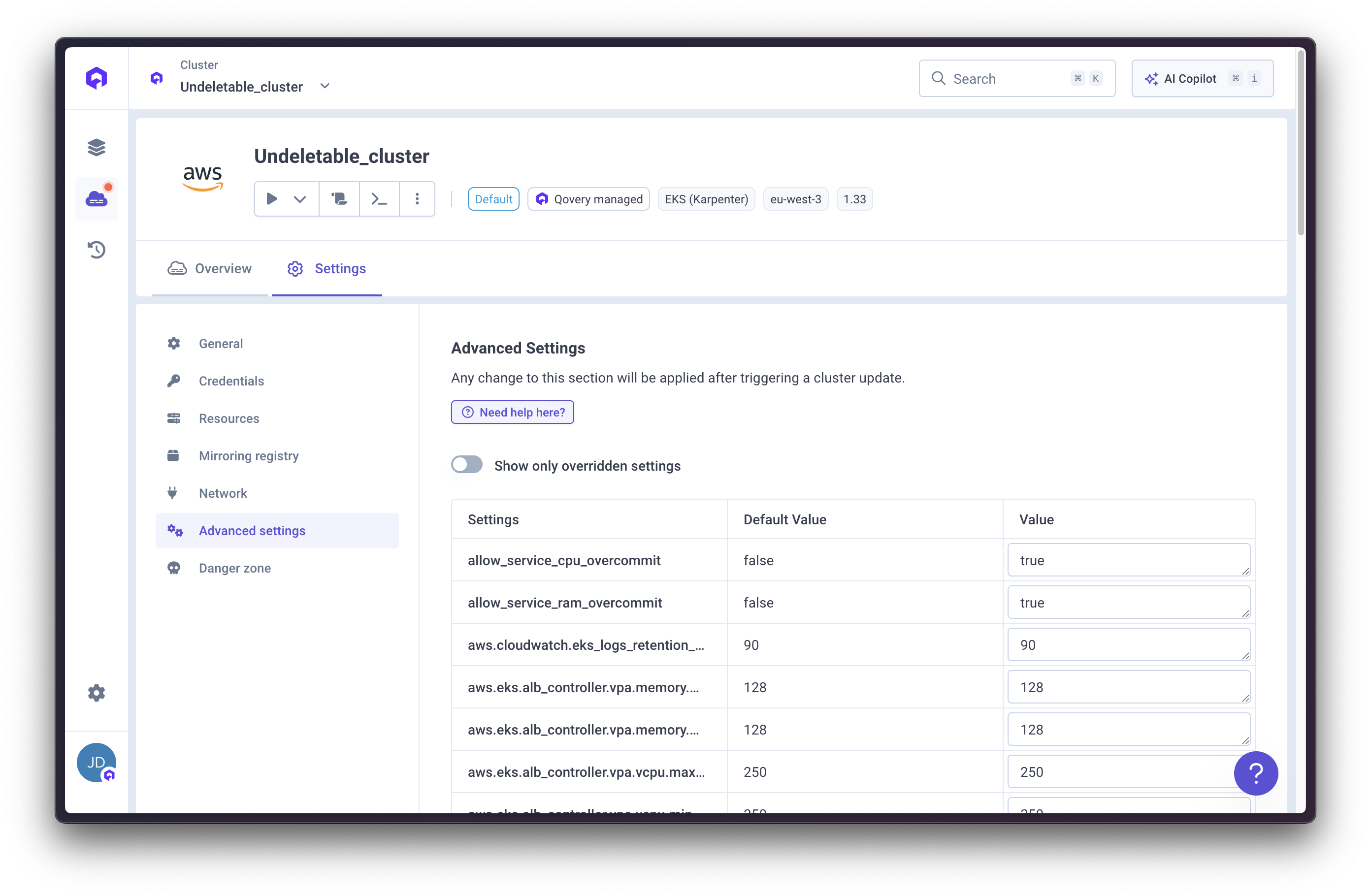
Configuring Cluster Advanced Settings
Via Qovery Console (Recommended)
The easiest way to configure cluster advanced settings is directly from the Qovery Console:Configure Settings
Browse and configure the advanced settings you need. Settings are organized by category for easy navigation.
Via Qovery API
You can also configure advanced settings using the Qovery API:Via Terraform
Use the Qovery Terraform Provider to manage cluster advanced settings as code:Cluster sizing
cluster.profile
Cloud Provider:string
Description: Defines the cluster sizing profile, which determines the default resource allocation and performance characteristics of the cluster.
Choosing a larger profile may incur higher costs but provides better performance and capacity for workloads.
Here are detailed insights to help you choose the right profile:
Small: Suitable for development, testing, or small-scale applications with low resource demands.- 3-5 nodes | 12-20 vCPUs | 24-40 GB RAM | ~50-100 pods
- Node size: 2-4 vCPUs, 4-8 GB RAM per node
- Use cases: Development, staging, small internal tools
Medium: A balanced option for moderate workloads, suitable for most production applications.- 6-10 nodes | 48-80 vCPUs | 96-160 GB RAM | ~200-400 pods
- Node size: 4-8 vCPUs, 8-16 GB RAM per node
- Use cases: Small to medium production apps, multi-tenant dev environments
Large: Designed for high-traffic applications or workloads requiring significant resources.- 11-20 nodes | 176-320 vCPUs | 352-640 GB RAM | ~500-1000 pods
- Node size: 8-16 vCPUs, 16-32 GB RAM per node
- Use cases: Enterprise production applications, microservices architectures
ExtraLarge: Ideal for enterprise-level applications with intensive resource needs and high availability requirements.- 20+ nodes | 400+ vCPUs | 800+ GB RAM | 1000+ pods
- Node size: 16-32+ vCPUs, 32-64+ GB RAM per node
- Use cases: Large-scale production, ML/AI workloads, intensive data processing
Small, Medium, Large, ExtraLarge
Default Value: Medium
Logs
aws.cloudwatch.eks_logs_retention_days
Cloud Provider:integer
Description: Maximum retention days in CloudWatch for EKS logs.
Valid values: 0, 1, 3, 5, 7, 14, 30, 60, 90, 120, 150, 180, 365, 400, 545, 731, 1827, 2192, 2557, 2922, 3288, 3653
Default Value: 90
aws.vpc.enable_s3_flow_logs
Cloud Provider:boolean
Description: Enable flow logs on the cluster VPC and store them in an S3 bucket. VPC flow logs capture information about IP traffic going to and from network interfaces in your VPC.
Use Case: Required for compliance frameworks (SOC 2, PCI-DSS, HIPAA) that mandate network traffic logging. Also useful for security investigations and troubleshooting connectivity issues.
Default Value: false
aws.vpc.flow_logs_retention_days
Cloud Provider:integer
Description: Set the number of retention days for flow logs. Set to 0 for unlimited retention.
Default Value: 365
aws.vpc.enable_nat_gateway_secondary_eip
Cloud Provider:boolean
Description: Enable a secondary Elastic IP (EIP) per NAT Gateway. When enabled, each of the 3 NAT Gateways in your VPC receives an additional EIP, doubling the number of outbound public IP addresses from 3 to 6. This is useful when your workloads interact with external services that have IP-based rate limits — more IPs means higher aggregate limits.
Default Value: false
loki.log_retention_in_week
Cloud Provider:integer
Description: Maximum retention period (in weeks) for application logs collected by Loki and displayed in the Qovery console log viewer. Retention is enforced both at the Loki compactor level and via object storage lifecycle policies.
Use Case: Increase for compliance requirements or debugging long-running issues. Decrease to save storage costs on the underlying object storage bucket.
Default Value: 12 (84 days)
loki.deployment_mode
Cloud Provider:enum (single_binary, simple_scalable)
Description: Loki deployment topology. single_binary runs Loki as a single pod; simple_scalable splits it into separate write, read, and backend components for larger clusters.
Use Case: Switch to simple_scalable when the cluster ingests more logs than a single Loki pod can handle. Keep the default for small to medium clusters.
Default Value: single_binary
loki.single_binary.cpu_request_m
Cloud Provider:integer
Description: CPU request (in milli-CPU) for the Loki pod when running in single_binary mode.
Default Value: 300
loki.single_binary.cpu_limit_m
Cloud Provider:integer
Description: CPU limit (in milli-CPU) for the Loki pod when running in single_binary mode.
Default Value: 8000
loki.single_binary.memory_request_mib
Cloud Provider:integer
Description: Memory request (in MiB) for the Loki pod when running in single_binary mode.
Default Value: 1024
loki.single_binary.memory_limit_mib
Cloud Provider:integer
Description: Memory limit (in MiB) for the Loki pod when running in single_binary mode.
Default Value: 2048
loki.write.cpu_request_m
Cloud Provider:integer
Description: CPU request (in milli-CPU) for the Loki write component when running in simple_scalable mode.
Default Value: 300
loki.write.cpu_limit_m
Cloud Provider:integer
Description: CPU limit (in milli-CPU) for the Loki write component when running in simple_scalable mode.
Default Value: 8000
loki.write.memory_request_mib
Cloud Provider:integer
Description: Memory request (in MiB) for the Loki write component when running in simple_scalable mode.
Default Value: 1024
loki.write.memory_limit_mib
Cloud Provider:integer
Description: Memory limit (in MiB) for the Loki write component when running in simple_scalable mode.
Default Value: 2048
loki.read.cpu_request_m
Cloud Provider:integer
Description: CPU request (in milli-CPU) for the Loki read component when running in simple_scalable mode.
Default Value: 300
loki.read.cpu_limit_m
Cloud Provider:integer
Description: CPU limit (in milli-CPU) for the Loki read component when running in simple_scalable mode.
Default Value: 8000
loki.read.memory_request_mib
Cloud Provider:integer
Description: Memory request (in MiB) for the Loki read component when running in simple_scalable mode.
Default Value: 1024
loki.read.memory_limit_mib
Cloud Provider:integer
Description: Memory limit (in MiB) for the Loki read component when running in simple_scalable mode.
Default Value: 2048
loki.backend.cpu_request_m
Cloud Provider:integer
Description: CPU request (in milli-CPU) for the Loki backend component when running in simple_scalable mode.
Default Value: 300
loki.backend.cpu_limit_m
Cloud Provider:integer
Description: CPU limit (in milli-CPU) for the Loki backend component when running in simple_scalable mode.
Default Value: 8000
loki.backend.memory_request_mib
Cloud Provider:integer
Description: Memory request (in MiB) for the Loki backend component when running in simple_scalable mode.
Default Value: 1024
loki.backend.memory_limit_mib
Cloud Provider:integer
Description: Memory limit (in MiB) for the Loki backend component when running in simple_scalable mode.
Default Value: 2048
gcp.vpc.enable_flow_logs
Cloud Provider:boolean
Description: Enable VPC flow logs on the cluster VPC (on each VPC subnetwork). See GCP VPC logs flow documentation.
Default Value: false
gcp.vpc.flow_logs_sampling
Cloud Provider:float
Description: Set VPC logs flow sampling percentage. Value should be within 0.0 (no sampling) to 1.0 (all logs) range.
Default Value: 0.0
object_storage.enable_logging
Cloud Provider:boolean
Description: Activate cluster buckets logging into a <bucket>-log bucket. See documentation for AWS and GCP.
Default Value: false
DNS
dns.coredns.extra_config
Cloud Provider:string
Description: Additional configuration to add to CoreDNS. This can be used to customize DNS resolution rules on the cluster. The value is appended to the default CoreDNS Corefile.
Use Case: Forward specific domains to internal DNS servers (split-horizon DNS), resolve private hosted zones, or add custom caching rules.
Default Value: null
Examples:
- Forward to internal DNS
- Forward to public resolver
Route queries for your internal domain to a private DNS server:
Image Registry
registry.image_retention_time
Cloud Provider:integer
Description: Allows you to specify an amount in seconds after which images in the default registry are deleted.
Changing this setting will only affect new ECR repositories created after the change. Existing repositories will not be affected.
31536000 (1 year)
registry.mirroring_mode
Cloud Provider:string
Description: Allows you to specify the image mirroring mode to be used for each image deployed on this cluster.
Valid values:
Service— each service gets its own mirror repository (qovery-mirror-{service_id}). Provides better isolation but creates more repositories. Works on all cluster types.Cluster— all services in the cluster share a single mirror repository (qovery-mirror-cluster-{cluster_id}). Fewer repositories, but requires registry lifecycle policy support for automated image cleanup.
Service
cloud_provider.container_registry.tags
Cloud Provider:Map<String, String>
Description: Add additional tags on the cluster dedicated registry.
Default Value: {}
Example:
Network - Load Balancer
aws.eks.enable_alb_controller
Cloud Provider:boolean
Description: Enable the AWS ALB controller to manage the load balancer for the cluster.
Use Case: For custom VPCs (Qovery Managed VPC does not require these), you need to add labels to subnets: kubernetes.io/role/elb=1 on public subnets, kubernetes.io/role/internal-elb=1 on private subnets, and kubernetes.io/cluster/<cluster-name>=shared on all subnets.
Default Value: true
aws.eks.alb_controller.replicas
Cloud Provider:integer
Description: Sets AWS ALB controller number of replicas. For production clusters, it’s recommended to have at least 2 replicas for high availability.
Default Value: 2
aws.eks.alb_controller.vpa.vcpu.min_in_milli_cpu
Cloud Provider:integer
Description: Sets AWS ALB controller VPA (vertical pod autoscaling) vCPU minimum value in milli CPU.
Default Value: 250
aws.eks.alb_controller.vpa.vcpu.max_in_milli_cpu
Cloud Provider:integer
Description: Sets AWS ALB controller VPA (vertical pod autoscaling) vCPU maximum value in milli CPU.
Default Value: 250
aws.eks.alb_controller.vpa.memory.min_in_mib
Cloud Provider:integer
Description: Sets AWS ALB controller VPA (vertical pod autoscaling) memory minimum value in mebibyte.
Default Value: 128
aws.eks.alb_controller.vpa.memory.max_in_mib
Cloud Provider:integer
Description: Sets AWS ALB controller VPA (vertical pod autoscaling) memory maximum value in mebibyte.
Default Value: 128
aws.eks.alb_controller.load-balancer-source-ranges
Cloud Provider:list of cidr string
Description: Specifies the CIDRs that are allowed to access the NLB. https://kubernetes-sigs.github.io/aws-load-balancer-controller/v3.2/guide/service/annotations/#lb-source-ranges
Default Value: []
Example: ["10.0.0.0/8", "192.168.0.0/16"]
aws.eks.alb_controller.load-balancer-scheme
Cloud Provider:string
Description: Specify if the load balancer is internet-facing and reachable from internet. Or if the load balancer is internal and reachable only from the cluster VPC.
Default Value: internet-facing
load_balancer.size
Cloud Provider:string
Description: Allows you to specify the load balancer size in front of your cluster.
Valid values: lb-s (200 Mbps), lb-gp-m (500 Mbps), lb-gp-l (1 Gbps), lb-gp-xl (4 Gbps)
Default Value: lb-s
Network - NGINX Ingress
nginx.vcpu.request_in_milli_cpu
Cloud Provider:integer
Description: vCPU request value in millicores assigned to NGINX pods.
Default Value: 200
nginx.vcpu.limit_in_milli_cpu
Cloud Provider:integer
Description: vCPU limit value in millicores assigned to NGINX pods.
Default Value: 700
nginx.memory.request_in_mib
Cloud Provider:integer
Description: Memory request value in MiB assigned to NGINX pods.
Default Value: 768
nginx.memory.limit_in_mib
Cloud Provider:integer
Description: Memory limit value in MiB assigned to NGINX pods.
Default Value: 768
nginx.hpa.cpu_utilization_percentage_threshold
Cloud Provider:integer
Description: HPA CPU threshold in percentage assigned to NGINX deployment.
Default Value: 50
nginx.hpa.min_number_instances
Cloud Provider:integer
Description: Minimum number of NGINX replicas for horizontal pod autoscaling.
Default Value: 2
nginx.hpa.max_number_instances
Cloud Provider:integer
Description: Maximum number of NGINX replicas for horizontal pod autoscaling.
Default Value: 25
nginx.controller.enable_client_ip
Cloud Provider:boolean
Description: Enables ngx_http_realip_module module to get the real client IP address.
Default Value: false
nginx.controller.enable_compression
Cloud Provider:boolean
Description: Enables compression (Brotli) for HTTP responses. When disabled, content will not be compressed, which may increase bandwidth usage but reduce CPU load.
Default Value: true
nginx.controller.use_forwarded_headers
Cloud Provider:boolean
Description: Passes incoming X-Forwarded-For header upstream. See documentation.
Default Value: false
nginx.controller.compute_full_forwarded_for
Cloud Provider:boolean
Description: Append the remote address to the X-Forwarded-For header instead of replacing it. See documentation.
Default Value: false
nginx.controller.log_format_upstream
Cloud Provider:string
Description: Allows to customize NGINX log-format.
Default Value: null
nginx.controller.log_format_escaping
Cloud Provider:string
Description: Allows to customize NGINX log-format-escaping setting.
Valid values: Default, JSON, None
Default Value: Default
nginx.controller.http_snippet
Cloud Provider:string
Description: Allows to customize NGINX http-snippet configuration. Used for cluster-level NGINX configuration that applies to all services.
Use Case: See Rate Limiting Guide for practical examples.
Default Value: null
nginx.controller.server_snippet
Cloud Provider:string
Description: Allows to customize NGINX server-snippet configuration. Used for server-level NGINX configuration.
Use Case: See Rate Limiting Guide for practical examples.
Default Value: null
nginx.controller.limit_request_status_code
Cloud Provider:integer
Description: Allows to customize NGINX limit-req-status-code. Commonly set to 429 (Too Many Requests) for rate limiting.
Default Value: null (defaults to 503)
nginx.controller.custom_http_errors
Cloud Provider:string
Description: Allows to customize NGINX custom-http-errors.
Default Value: null
Example: "404,503"
nginx.default_backend.enabled
Cloud Provider:boolean
Description: Allows enabling the default_backend for NGINX.
Default Value: false
nginx.default_backend.image_repository
Cloud Provider:string
Description: Specifies the Docker image repository used for the default_backend.
Default Value: null
nginx.default_backend.image_tag
Cloud Provider:string
Description: Defines the image tag used by default_backend.
Default Value: null
Network - Gateway API
k8s.deploy_api_gateway
Cloud Provider:boolean
Description: Deploys Gateway API resources on the cluster if true.
Default Value: false
k8s.use_api_gateway
Cloud Provider:boolean
Description: Makes Gateway API the default routing component.
Default Value: false
envoy.hpa.cpu_average_utilization_percentage_threshold
Cloud Provider:float
Description: HPA CPU average utilization threshold for the Envoy data plane managed by Envoy Gateway, expressed as a value between 0.0 and 1.0 (e.g., 0.8 for 80%). When CPU usage exceeds this threshold, Kubernetes scales the Envoy proxy replicas serving traffic. This setting applies to EnvoyProxy.spec.provider.kubernetes.envoyHpa. Learn more in the EnvoyProxy HPA documentation.
Valid values: 0.0 to 1.0
Default Value: null (uses Kubernetes default behavior)
envoy.hpa.memory_average_utilization_percentage_threshold
Cloud Provider:float
Description: HPA memory average utilization threshold for the Envoy data plane managed by Envoy Gateway, expressed as a value between 0.0 and 1.0 (e.g., 0.8 for 80%). When memory usage exceeds this threshold, Kubernetes scales the Envoy proxy replicas serving traffic. This setting applies to EnvoyProxy.spec.provider.kubernetes.envoyHpa. Learn more in the EnvoyProxy HPA documentation.
Valid values: 0.0 to 1.0
Default Value: null (uses Kubernetes default behavior)
envoy.hpa.min_number_instances
Cloud Provider:integer
Description: Minimum number of Envoy data-plane replicas managed by Envoy Gateway for horizontal pod autoscaling. This ensures a baseline level of availability and traffic-serving capacity. Must be less than or equal to envoy.hpa.max_number_instances.
Default Value: 2 for production clusters, 1 for non-production clusters
envoy.hpa.max_number_instances
Cloud Provider:integer
Description: Maximum number of Envoy data-plane replicas managed by Envoy Gateway for horizontal pod autoscaling. This sets an upper limit on traffic-serving scale and resource consumption. Must be greater than or equal to envoy.hpa.min_number_instances.
Default Value: 25
envoy.gateway.hpa.cpu_average_utilization_percentage_threshold
Cloud Provider:float
Description: HPA CPU average utilization threshold for the Envoy Gateway control-plane deployment, expressed as a value between 0.0 and 1.0 (e.g., 0.8 for 80%). When CPU usage exceeds this threshold, Kubernetes scales the envoy-gateway controller deployment. This setting applies to the Gateway Helm chart HPA for the control plane.
Valid values: 0.0 to 1.0
Default Value: null (uses Kubernetes default behavior)
envoy.gateway.hpa.memory_average_utilization_percentage_threshold
Cloud Provider:float
Description: HPA memory average utilization threshold for the Envoy Gateway control-plane deployment, expressed as a value between 0.0 and 1.0 (e.g., 0.8 for 80%). When memory usage exceeds this threshold, Kubernetes scales the envoy-gateway controller deployment. This setting applies to the Gateway Helm chart HPA for the control plane.
Valid values: 0.0 to 1.0
Default Value: null (uses Kubernetes default behavior)
envoy.gateway.hpa.min_number_instances
Cloud Provider:integer
Description: Minimum number of Envoy Gateway control-plane replicas for horizontal pod autoscaling. This ensures baseline controller availability for reconciliation and configuration updates. Must be less than or equal to envoy.gateway.hpa.max_number_instances.
Default Value: 2 for production clusters, 1 for non-production clusters
envoy.gateway.hpa.max_number_instances
Cloud Provider:integer
Description: Maximum number of Envoy Gateway control-plane replicas for horizontal pod autoscaling. This sets an upper limit on controller scaling and resource consumption. Must be greater than or equal to envoy.gateway.hpa.min_number_instances.
Default Value: 5
envoy.vcpu.request_in_milli_cpu
Cloud Provider:integer
Description: vCPU request value in millicores assigned to Envoy Gateway pods. This defines the minimum CPU resources guaranteed for each pod. Must be less than or equal to envoy.vcpu.limit_in_milli_cpu.
Default Value: 100
envoy.vcpu.limit_in_milli_cpu
Cloud Provider:integer
Description: vCPU limit value in millicores assigned to Envoy Gateway pods. This defines the maximum CPU resources that each pod can consume. Must be greater than or equal to envoy.vcpu.request_in_milli_cpu.
Default Value: 1000
envoy.memory.request_in_mib
Cloud Provider:integer
Description: Memory request value in MiB assigned to Envoy Gateway pods. This defines the minimum memory resources guaranteed for each pod. Must be less than or equal to envoy.memory.limit_in_mib.
Default Value: 256
envoy.memory.limit_in_mib
Cloud Provider:integer
Description: Memory limit value in MiB assigned to Envoy Gateway pods. This defines the maximum memory resources that each pod can consume. Must be greater than or equal to envoy.memory.request_in_mib.
Default Value: 1024
envoy.gateway_api.http_request_timeout_seconds
Cloud Provider:integer (unsigned)
Description: Sets the default request timeout in seconds for Envoy Gateway BackendTrafficPolicy. This value is used when services do not define network.gateway_api.http_request_timeout_seconds.
Use Case: Configure a cluster-wide timeout baseline for Gateway API routes while still allowing service-level overrides when needed.
Default Value: null (uses Envoy Gateway default)
Example:
envoy.gateway_api.http_connection_idle_timeout_seconds
Cloud Provider:integer (unsigned)
Description: Sets the default idle connection timeout in seconds for Envoy Gateway BackendTrafficPolicy. This value is used when services do not define network.gateway_api.http_connection_idle_timeout_seconds.
Use Case: Apply a cluster-wide default for idle HTTP backend connections while keeping service-level tuning available.
Default Value: null (uses Envoy Gateway default)
Example:
envoy.gateway_api.http_stream_idle_timeout_seconds
Cloud Provider:integer (unsigned)
Description: Sets the stream idle timeout in seconds for Envoy Gateway ClientTrafficPolicy at gateway level. A stream is considered idle when no upstream or downstream data is exchanged during the configured period. This maps to Envoy stream_idle_timeout behavior. Learn more in the Envoy timeout documentation.
Use Case: Keep long-running streaming responses alive while still terminating genuinely stalled streams.
Default Value: null (uses Envoy Gateway default)
Example:
envoy.gateway_api.http_max_stream_duration_seconds
Cloud Provider:integer (unsigned)
Description: Sets the default maximum stream duration in seconds for Envoy Gateway BackendTrafficPolicy. This value is used when services do not define network.gateway_api.http_max_stream_duration_seconds. This maps to Envoy max_stream_duration behavior. Learn more in the Envoy timeout documentation.
Use Case: Put a hard upper bound on stream lifetime while still allowing long-running active streams below that limit.
Default Value: null (uses Envoy Gateway default)
Example:
envoy.gateway_api.retry.num_retries
Cloud Provider:integer (unsigned)
Description: Sets the default retry attempt count for Gateway API traffic at cluster level. This value is used when services do not define network.gateway_api.retry.num_retries.
Use Case: Define a consistent retry baseline for all services in the cluster while still allowing per-service overrides.
Default Value: 2
Example:
envoy.gateway_api.retry.retry_on
Cloud Provider:string (CSV)
Description: Defines default retry conditions at cluster level (for example connect-failure, reset, refused-stream, retriable-status-codes). Used when services do not define network.gateway_api.retry.retry_on.
Use Case: Apply consistent retry triggers across services while allowing local service overrides when needed.
Default Value: "connect-failure,reset,refused-stream"
Example:
envoy.gateway_api.retry.http_status_codes
Cloud Provider:string (CSV of HTTP codes)
Description: Defines default HTTP status codes to retry at cluster level. Codes must be integers in range 100..599. Used when services do not define network.gateway_api.retry.http_status_codes.
Use Case: Limit retries to specific response codes across services (for example 503,504) without configuring each service separately.
Default Value: null (unset)
Example:
envoy.gateway_api.retry.per_try_timeout_seconds
Cloud Provider:integer (unsigned, > 0)
Description: Sets the default timeout in seconds for each retry attempt. Used when services do not define network.gateway_api.retry.per_try_timeout_seconds.
Use Case: Cap each retry attempt cluster-wide to reduce tail latency and avoid long blocked attempts.
Default Value: null (unset)
Example:
envoy.client_ip_detection.x_forwarded_for.number_trusted_hops
Cloud Provider:integer
Description: Number of trusted hops in the X-Forwarded-For header for client IP detection. This setting determines how many proxy hops to trust when extracting the real client IP address. See Envoy Gateway documentation for more details.
For customers migrating from NGINX: This replaces the NGINX
use_forwarded_headers and compute_full_forwarded_for settings. Envoy uses a hop count model, but null (unset) and 0 are not equivalent in Qovery.- Leave as
null(unset) to keep direct connection IP detection (useRemoteAddress = true). This is the safest migration option when existing RBAC / IP whitelist logic depends on source IP from the TCP peer. - Set to
0to enable XFF-based detection withuseRemoteAddress = falseandxffNumTrustedHops = 0. - Set to
1if your traffic passes through 1 trusted proxy (e.g., AWS ALB only) - Set to
2if your traffic passes through 2 trusted proxies (e.g., CloudFront → ALB)
number_trusted_hops value | xffNumTrustedHops | useRemoteAddress |
|---|---|---|
absent (null) | — | true |
0 | 0 | false |
1 | 0 | false |
2 | 1 | false |
3 | 2 | false |
0 and 1 therefore behave the same from an XFF trust perspective (xffNumTrustedHops = 0).
NGINX mapping note: nginx.controller.use_forwarded_headers = false maps closest to leaving envoy.client_ip_detection.x_forwarded_for.number_trusted_hops unset (null), not to setting it to 0.
Example: If a request arrives with X-Forwarded-For: client-ip, proxy1-ip, proxy2-ip:
- with
number_trusted_hops: 2(mapped toxffNumTrustedHops: 1), detected client IP isproxy1-ip - with
number_trusted_hops: 3(mapped toxffNumTrustedHops: 2), detected client IP isclient-ip
null (uses Envoy default behavior)
envoy.client_ip_detection.x_forwarded_for.trusted_cidrs
Cloud Provider:array[string]
Description: List of trusted CIDR ranges used to evaluate X-Forwarded-For and determine the original client IP address. This is the CIDR-based strategy for Envoy client IP detection. See Envoy Gateway documentation.
How to configure:
- Add your trusted proxy CIDRs (for example the CIDRs used by your edge/load balancers)
- Keep the list empty to disable this strategy
- Use this strategy when proxy hop count is variable but source proxy networks are known
[]
envoy.log_format
Cloud Provider:string (JSON format)
Description: Custom log format for Envoy Gateway access logs. Qovery only allows JSON format as it enables all the Qovery capabilities for application logging and tracing. The value must be a JSON object (provided as a string) with Envoy command operators. See Envoy Gateway access logging documentation for available format variables and configuration options.
For customers migrating from NGINX: This replaces the NGINX
log_format_upstream setting. Envoy uses its own format string with command operators like %REQ(X-HEADER)%, %RESP(X-HEADER)%, and %DURATION% instead of NGINX’s $variable syntax.envoy.custom_certificate
Cloud Provider:string (JSON format)
Description: Allows you to upload your own TLS certificate that is going to be used by envoy when serving https traffic. Let’s encrypt is not going to be used to generate the cluster certificate. The certificate must be PEM encoded
Default Value: null
Example: Custom JSON format with certificate and key PEM encoded:
envoy.controller.custom_http_errors
Cloud Provider:list of integers
Description: List of HTTP status codes for which Envoy Gateway should serve custom error pages. When you specify a status code in this list, Envoy Gateway will intercept that error and serve a hardcoded HTML error page instead of passing through the upstream error response. Each HTTP error code has its own hardcoded HTML page built into Envoy Gateway.
The hardcoded error pages cannot be customized at this time. If you need to customize error pages for your use case, please contact us and we can extend this feature.
100 to 599
Default Value: null
Example: [404, 503, 502, 500] - This will serve custom hardcoded HTML pages for Not Found, Service Unavailable, Bad Gateway, and Internal Server Error responses.
envoy.controller.enable_compression
Cloud Provider:boolean
Description: Enables HTTP response compression in Envoy Gateway. When enabled, Envoy Gateway automatically compresses HTTP responses using multiple compression algorithms to reduce bandwidth usage and improve performance.
Compression algorithms enabled:
- Gzip - Compression level 6 (widely supported, good compression ratio)
- Brotli - Quality level 6 (better compression than Gzip, modern browsers)
- Zstd - Compression level 6 (fastest compression, newest standard)
Accept-Encoding header.
For customers migrating from NGINX: This replaces NGINX’s compression settings (
enable-brotli and use-gzip). The main difference is that Envoy Gateway adds Zstd as a third compression algorithm alongside Gzip and Brotli. All compression levels match NGINX defaults (level 6).true
envoy.default_backend.enabled
Cloud Provider:boolean
Description: Enables the default backend for Envoy Gateway. The default backend serves a generic error page for requests that don’t match any route.
Default Value: false
envoy.default_backend.image
Cloud Provider:string
Description: Specifies the Docker image used for the default backend.
Default Value: null
envoy.default_backend.tag
Cloud Provider:string
Description: Defines the image tag used by the default backend.
Default Value: null
Network - Database Access Control
database.postgresql.deny_any_access
Cloud Provider:boolean
Description: Deny any access to all PostgreSQL databases. When enabled, no CIDR (including allowed_cidrs) can reach the database — this is a hard deny that overrides everything.
Default Value: false
database.postgresql.allowed_cidrs
Cloud Provider:string
Description: List of allowed CIDR ranges for PostgreSQL database access. Only traffic from these CIDRs can reach the database. Ignored if database.postgresql.deny_any_access is true.
Default Value: ["0.0.0.0/0"]
Example: Restrict to your VPN and office IPs:
database.mysql.deny_any_access
Cloud Provider:boolean
Description: Deny any access to all MySQL databases. When enabled, this overrides allowed_cidrs.
Default Value: false
database.mysql.allowed_cidrs
Cloud Provider:string
Description: List of allowed CIDR ranges for MySQL database access. Ignored if database.mysql.deny_any_access is true.
Default Value: ["0.0.0.0/0"]
database.mongodb.deny_any_access
Cloud Provider:boolean
Description: Deny any access to all MongoDB databases. When enabled, this overrides allowed_cidrs.
Default Value: false
database.mongodb.allowed_cidrs
Cloud Provider:string
Description: List of allowed CIDR ranges for MongoDB database access. Ignored if database.mongodb.deny_any_access is true.
Default Value: ["0.0.0.0/0"]
database.redis.deny_any_access
Cloud Provider:boolean
Description: Deny any access to all Redis databases. When enabled, this overrides allowed_cidrs.
Default Value: false
database.redis.allowed_cidrs
Cloud Provider:string
Description: List of allowed CIDR ranges for Redis database access. Ignored if database.redis.deny_any_access is true.
Default Value: ["0.0.0.0/0"]
Service Resources
allow_service_cpu_overcommit
Cloud Provider:boolean
Description: Authorize CPU overcommit (limit > request) for services deployed within this cluster. When enabled, pods can burst above their CPU request up to the configured limit when spare capacity is available on the node.
Use Case: Once enabled, you can update the service advanced setting resources.override.limit.cpu_in_milli to set a CPU limit higher than the request.
Default Value: false
allow_service_ram_overcommit
Cloud Provider:boolean
Description: Authorize memory overcommit (limit > request) for services deployed within this cluster. When enabled, pods can use more memory than their request up to the configured limit.
Use Case: Once enabled, you can update the service advanced setting resources.override.limit.ram_in_mib to set a memory limit higher than the request.
Default Value: false
IAM & Security
aws.iam.enable_admin_group_sync
Cloud Provider:boolean
Description: Enable IAM admin group sync. See IAM permissions setup.
Default Value: true
aws.iam.admin_group
Cloud Provider:string
Description: Allows you to specify the IAM group name associated with the Qovery user. Configure IAM group permissions for cluster access.
Default Value: Admins
aws.iam.enable_sso
Cloud Provider:boolean
Description: Enable SSO sync allowing IAM users to connect to cluster using SSO.
Default Value: false
aws.iam.sso_role_arn
Cloud Provider:string
Description: Allows you to specify the SSO role ARN to be used to connect to your cluster.
Default Value: ""
aws.eks.encrypt_secrets_kms_key_arn
Cloud Provider:string
Description: Allows you to activate KMS encryption of your Kubernetes secrets. Specify the key ARN of your AWS KMS key.
Default Value: null
k8s.api.allowed_public_access_cidrs
Cloud Provider:string
Description: Contains additional CIDRs that should be whitelisted to access the Kubernetes API. Use this to allow your team or CI/CD pipelines to reach the K8s API when qovery.static_ip_mode is enabled.
qovery.static_ip_mode should be set to true to make this setting effective.[]
Example:
Miscellaneous
aws.eks.ec2.metadata_imds
Cloud Provider:string
Description: Specify the IMDS version you want to use.
Valid values:
required— IMDSv2 only (recommended). Forces all metadata requests to use session tokens, which protects against SSRF attacks that try to steal instance credentials.optional— IMDSv1 and v2. Use only if you have legacy workloads that don’t support IMDSv2.
required
aws.eks.ec2.ami
Cloud Provider:string
Description: Specify the AMI you want to use for EKS worker nodes (Karpenter only).
Valid values:
AmazonLinux2(Deprecated, not working after Kubernetes 1.32)AmazonLinux2023(Default Amazon AMI, recommended)Bottlerocket(Focuses on security and maintainability)ami-xxx— A custom AMI ID (e.g.ami-0123456789abcdef0). Assumes AL2023-based by default.my-custom-ami-*— A custom AMI name pattern with optional wildcards. Assumes AL2023-based by default.al2:ami-xxxoral2:my-ami-*— A custom AMI based on Amazon Linux 2.al2023:ami-xxxoral2023:my-ami-*— A custom AMI based on Amazon Linux 2023 (explicit).bottlerocket:ami-xxxorbottlerocket:my-ami-*— A custom AMI based on Bottlerocket.
Custom AMIs without a family prefix are assumed to be AL2023-based. Use a prefix (
al2:, al2023:, bottlerocket:) to specify the base OS so that Karpenter generates the correct bootstrap configuration. This setting only applies to Karpenter-managed nodes (not managed node groups). GPU nodes are not affected by this setting.AmazonLinux2023
aws.metrics_server.replicas
Cloud Provider:integer
Description: Specify the number of replicas for the metrics-server pod. Set to 2 or more in production for high availability.
Default Value: 1
qovery.static_ip_mode
Cloud Provider:boolean
Description: Enable the static IP mode for the Qovery control plane and automatically activate the private endpoint on the Kubernetes API and add the Qovery IP to the CIDR whitelist.
DockerHub credentials are required to activate this feature. Configure them in Organization settings > Container registry. Why? DockerHub has a rate limit by IP. Since the Qovery control plane will be seen as a single IP, you need authenticated access to increase the limit.
false
Storage
storageclass.fast_ssd
Cloud Provider:string
Description: Specify the Kubernetes storageClass to be used for storage attached to your container databases and applications. Override this if you need a custom storageClass (e.g., for encryption, specific IOPS, or a different disk type).
Default Value: "" (empty — each cloud provider uses its own default)
When left empty, Qovery uses the following storageClasses per provider:
| Cloud Provider | StorageClass | Disk Type |
|---|---|---|
| AWS | aws-ebs-gp3-0 | General Purpose SSD (GP3) |
| GCP | gcp-pd-balanced | Balanced persistent disk |
| Azure | azure-standard-ssd-zrs | Standard SSD with zone-redundant storage |
| Scaleway | scw-sbv-ssd-0 | Block Storage SSD |
AWS GP2 → GP3 migration: If your cluster still uses
aws-ebs-gp2-0 (legacy), we recommend migrating to aws-ebs-gp3-0. GP3 offers better baseline performance (3,000 IOPS and 125 MB/s included) at a lower cost than GP2. Set storageclass.fast_ssd to aws-ebs-gp3-0 and redeploy your cluster.GCP also supports
gcp-pd-ssd for higher IOPS. Azure supports azure-premium-lrs, azure-premium-v2-lrs, azure-premium-zrs, azure-ultra-ssd-lrs, and azure-standard-ssd-lrs.aws.eks.enable_efs_addon
Cloud Provider:boolean
Description: Enable the AWS EFS CSI driver EKS add-on to provision EFS-backed persistent volumes on the cluster.
When enabled, Qovery automatically provisions:
- The EFS CSI driver as a managed EKS add-on
- An encrypted EFS file system dedicated to the cluster
- A security group allowing NFS (port 2049) from the VPC
- Mount targets in each availability zone used by the cluster
- The required IAM roles and policies (IRSA)
- A StorageClass named
aws-efsfor dynamic provisioning via EFS access points
EFS provides shared, multi-AZ, ReadWriteMany storage — ideal for workloads that need to share files across multiple pods or nodes (e.g. CMS uploads, shared config, ML datasets).
Using EFS with Helm charts
Once the setting is enabled and the cluster is deployed, theaws-efs StorageClass is available. Create a PersistentVolumeClaim and mount it in your workload.
Step 1 — Create a PVC in your Helm chart templates:
false
aws.eks.efs.throughput_mode
Cloud Provider:string
Description: Controls how throughput is allocated for the EFS file system provisioned by the cluster.
| Mode | Throughput | Cost model | Best for |
|---|---|---|---|
elastic | Scales automatically up to 10 GiB/s read, 3 GiB/s write | Pay per GiB transferred (~0.06/GiB write) | Variable or unpredictable workloads |
bursting | Baseline 50 KiB/s per GiB stored, bursts up to 100 MiB/s | Included in storage cost (~$0.30/GiB-month) | Small file systems with occasional bursts |
provisioned | Fixed throughput you configure (1-3,072 MiB/s) | ~$6.00/MiB/s-month on top of storage | Steady, high-throughput workloads |
elastic, bursting
Default Value: elastic
aws.eks.efs.performance_mode
Cloud Provider:string
Description: Controls the I/O performance characteristics of the EFS file system.
| Mode | Latency | Max IOPS | Best for |
|---|---|---|---|
generalPurpose | Lowest (sub-ms) | Up to 55,000 read / 25,000 write | Web serving, CMS, home directories, most workloads |
maxIO | Slightly higher | No practical limit | Massively parallel big data, genomics, media processing |
generalPurpose, maxIO
Default Value: generalPurpose
aws.eks.efs.transition_to_ia
Cloud Provider:string
Description: Lifecycle policy that automatically moves files not accessed for the specified period to the Infrequent Access (IA) storage class.
| Storage class | Storage cost | Read cost | Write cost |
|---|---|---|---|
| Standard | ~$0.30/GiB-month | Included | Included |
| Infrequent Access | ~$0.016/GiB-month (~95% cheaper) | ~$0.01/GiB | ~$0.01/GiB |
"") to disable the lifecycle policy and keep all files in Standard storage.
Valid values: AFTER_1_DAY, AFTER_7_DAYS, AFTER_14_DAYS, AFTER_30_DAYS, AFTER_60_DAYS, AFTER_90_DAYS, "" (disabled)
Default Value: AFTER_30_DAYS
Next Steps
Service Advanced Settings
Configure service-level advanced settings
Rate Limiting Guide
Implement rate limiting with NGINX
IP Authorization Guide
Configure IP and header-based authorization
Cluster Management
Learn about cluster operations
Qovery API Reference
Explore the full Qovery API
Terraform Provider
Manage infrastructure as code
Kubernetes Changelog
Kubernetes cluster related updates

