What makes Qovery secure?
We have many articles on what Qovery is and how to use it, but today we cover a critical topic: security! Protecting your business is probably one of the most important criteria when choosing a product, and here at Qovery, we take this topic very seriously, so let me ease your mind and show you what makes Qovery's DevOps Automation Tool secure 🔒

Albane Tonnellier
April 4, 2022 · 4 min read
#Architecture Design
Our philosophy is “security by design” and here are some of the design choices that make Qovery one of the most reliable solutions out there.
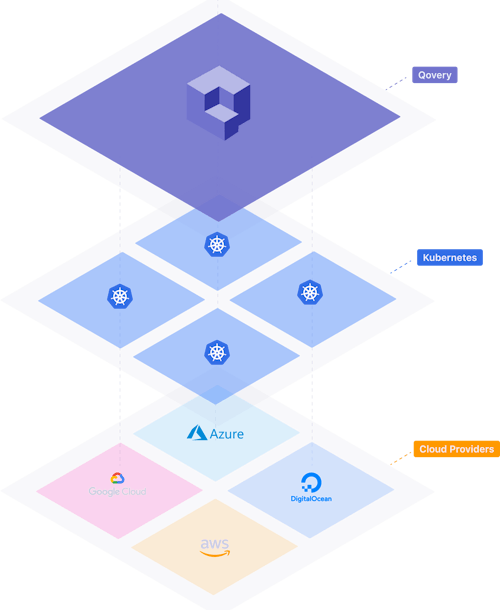
#Qovery runs on your AWS account
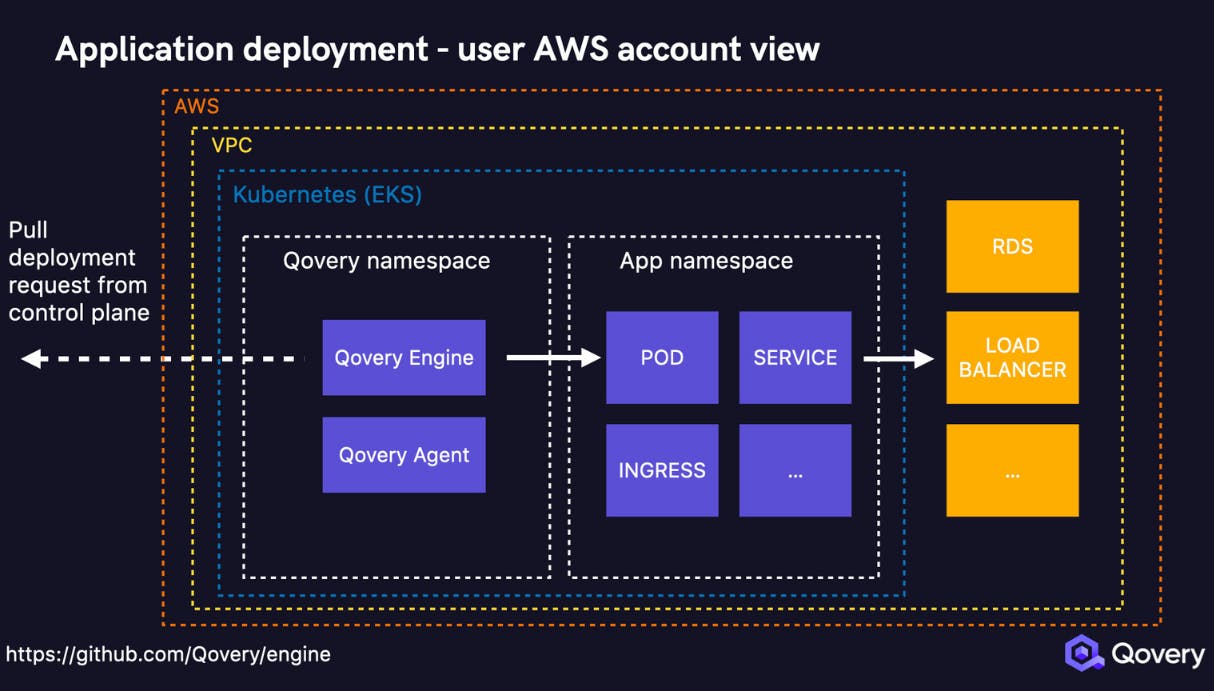
The first important point here is that Qovery runs on your AWS account and all the data that belongs to you stays there. Only a secure gRPC connection is initiated with the Qovery control plane to receive deployment instructions - we cover this point with more details below. This is an important design choice that brings maximum security since there is no hard dependency on our control plane. Even if qovery.com is down, your infrastructure is not impacted.
#Qovery Engine is open source
On top of encouraging innovation through collaboration, having an open-source Engine also means that everything is transparent so it won't leave security concerns.
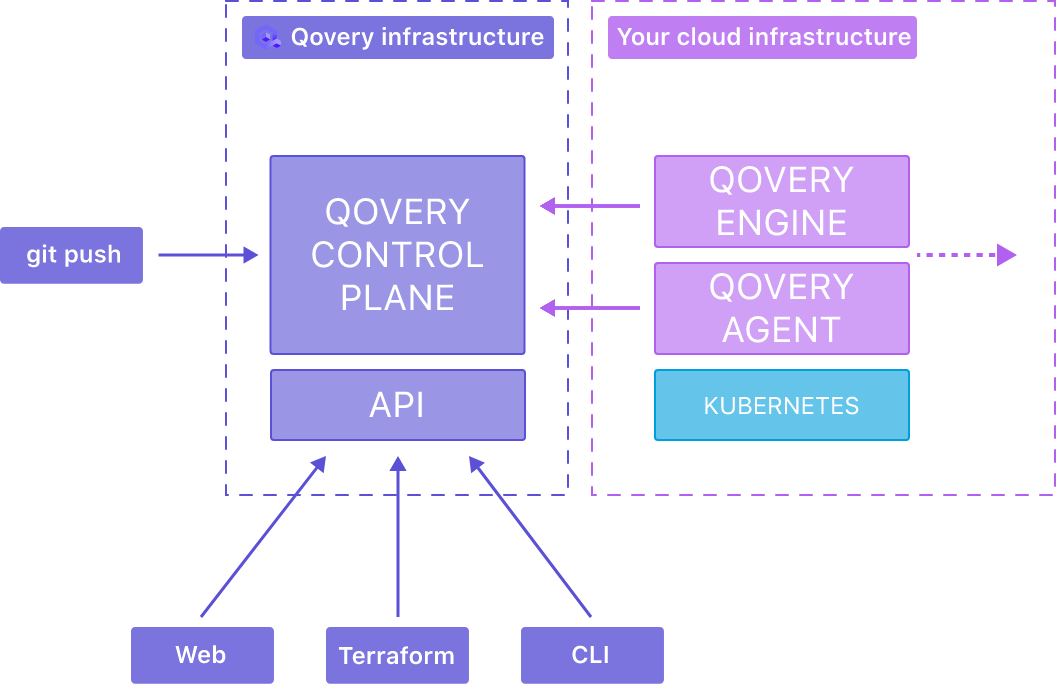
#Qovery Engine establishes the connection with the control plane
The Qovery Engine and the Qovery Agent receive remote instructions from the control plane via a secured gRPC/TLS connection initiated. Qovery infrastructure and your infrastructure are completely isolated from each other. Qovery has been designed to never impact your infrastructure in case of an outage and security breach, if you want extra information about it, our documentation is a great source of knowledge, along with this video that explains to you what it takes to build a developer platform.
#Qovery has limited access
As stated before, Qovery runs on your AWS account and we have limited access to the resources we manage for you on your AWS account - you can check the IAM permissions. In this tutorial, we explain to you how to set up your AWS account with Qovery and what is needed for us to install it.
#Authentification
Security starts as soon as you register or login into a product, here is how we keep you secure from the very beginning.
#User authentification (Github/Gitlab/Bitbucket) via Auth0
Auth0 is an authentication and authorization platform. When you create an account with Qovery, you will log in directly with your Github, Gitlab, or Bitbucket via Auth0, so you won’t need to create another account and spread your sensitive information even more.
#Two-step authentification (coming soon)
Two-factor authentication (2FA) is a security system that requires two separate, distinct forms of identification in order to access something. The first factor is a password, and the second commonly includes a text with a code sent to your smartphone.
To make Qovery even more secure, we are planning to implement it soon, to know where it’s going to be ready, follow our changelog that we publish every two weeks.
#AWS
AWS is working very hard to make their product as safe as possible; they created several ways to protect their customers from outside attacks, and here is how we make the most of their service.
#Deployment on AWS sub-account
After creating an AWS Organization, you can create separate and isolated sub AWS accounts while still under your current billing and management; this means that you can control who can see and change the most sensitive part of your AWS account and avoid human error.
We use a sub-account at Qovery for our product, and we also recommend you to use an AWS sub-account within your organization.
#Dedicated VPC
Amazon Virtual Private Cloud (Amazon VPC) enables you to launch AWS resources into a virtual network that you've defined. This virtual network closely resembles a traditional network that you'd operate in your own data center, with the benefits of using the scalable infrastructure of AWS. For more information on an AWS VPC, here is their documentation about it.
At Qovery, every cluster, database, and resources have their own VPC to avoid unwanted network communication with other VPCs. It is also possible to configure VPC peering with Qovery.
#Encryption
At Qovery, all the databases and disks are encrypted with AES-256. All credentials and secrets are also encrypted with AES-256 and salted.
#Qovery is HIPAA compliant
Since the 90s, when you run a company in the Healthcare industry in the US market, you must comply with the Health Insurance Portability and Accountability Act (HIPAA) Security Rule. Some of the security rules are directly linked to how you operate your organization; the others on how you manage your application data for your customers.
At Qovery, the infrastructures we deploy are HIPAA compliant, and if you want to know more about it, we explain in detail how to become HIPAA compliant on AWS in 2022.
#Road to SOC2 compliance
SOC 2 is a voluntary compliance standard for service organizations, developed by the American Institute of CPAs (AICPA), which specifies how organizations should manage customer data. The standard is based on the following Trust Services Criteria: security, availability, processing integrity, confidentiality, and privacy.
We are currently in the process of being SOC2 compliant this year as SOC 2 requirements indicate that an organization maintains a high level of information security.
#Wrapping up
When I told you that at Qovery, we don’t joke with security, I meant it! From encryption to HIPAA compliance, our product is architectured and secured. All of the extra time we take to follow those precautions and regulations makes it one of the most reliable solutions out there.
Your Favorite DevOps Automation Platform
Qovery is a DevOps Automation Platform Helping 200+ Organizations To Ship Faster and Eliminate DevOps Hiring Needs,
Try it out now!

Your Favorite DevOps Automation Platform
Qovery is a DevOps Automation Platform Helping 200+ Organizations To Ship Faster and Eliminate DevOps Hiring Needs,
Try it out now!
.jpg?ixlib=gatsbyFP&auto=compress%2Cformat&fit=max)