5 Tips For Managing Your Internal Developer Platform
Internal Developer Platforms (IDPs) have become the cornerstone of efficient development, serving as the central hub where development teams access the tools and resources necessary for coding, testing, deploying, and maintaining software applications. As software development continues to evolve rapidly, IDPs are crucial in maintaining a competitive edge. This introduction sets the stage for the technical insights that will follow, sharing 5 tips for effective Internal Developer Platform management.

Morgan Perry
October 11, 2023 · 13 min read
#Tip 1: Design for Scalability and Flexibility
When designing IDPs, it's crucial to consider scalability and flexibility. These principles form the foundation upon which an effective IDP is built. Organizations need to be prepared for growth and adapt their IDPs to meet the evolving demands of their development teams.
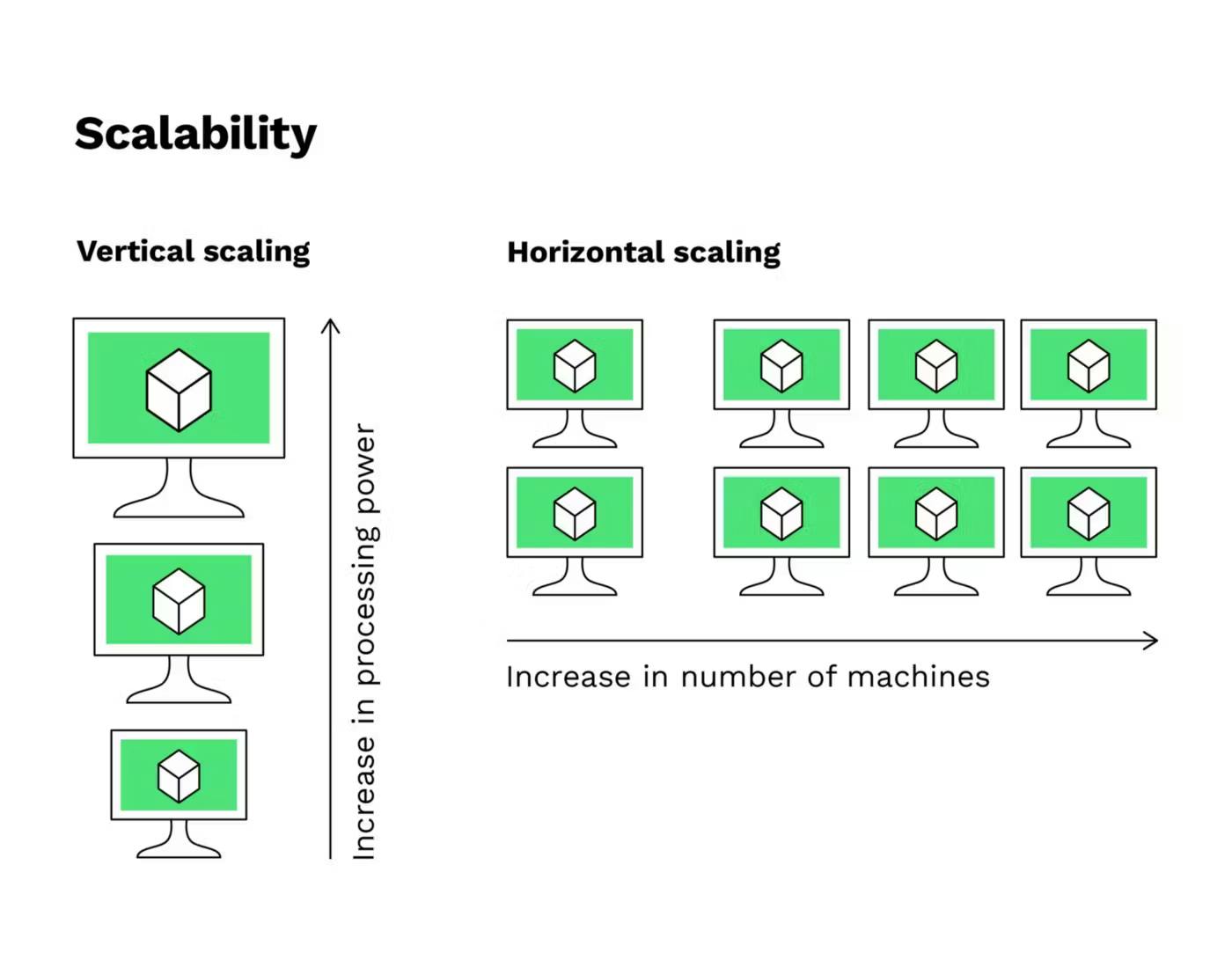
#Scalability
In a technical sense, scalability refers to an IDP's ability to handle increased loads and grow with the organization. This is critical for businesses of all sizes, as growth is an expected and desirable outcome. When designing your IDP, ensure that it can seamlessly accommodate more users, projects, and resources without significantly increasing complexity or cost.
A scalable IDP should be able to scale horizontally by adding more servers or containers as demand increases. If we take a microservices-based IDP as an example, it should be capable of swiftly spinning up new microservices to meet growing application requirements. Elasticity, another key concept, means that resources can be added or removed automatically based on demand. Technologies like container orchestration platforms (e.g., Kubernetes) play a pivotal role here. Kubernetes can automatically scale application instances up or down to maintain steady performance, ensuring your IDP can handle the ebb and flow of usage.
#Flexibility
Flexibility in IDP design pertains to the adaptability of the architecture and components to accommodate the ever-evolving needs of your development teams. A flexible IDP architecture should support variations in technology stacks, tools, and workflows that different projects or teams might prefer. It should be modular, allowing components to be added, replaced, or modified with relative ease.
For example, consider an IDP with a flexible architecture where you can easily swap out parts of your CI/CD pipeline. This flexibility means you can change your build tools, test frameworks, or deployment strategies as your project's requirements evolve. Microservices-based architectures exemplify flexibility. They allow you to build and deploy microservices using the most suitable technology for the task, ensuring that you're not locked into a single, rigid tech stack.
A flexible IDP doesn't just allow you to adjust technology but also to tailor processes to different projects. It recognizes that a large data analytics project might have different requirements than a front-end web application. Flexibility empowers development teams to choose the right tools and methodologies to optimize their workflows while adhering to the organization's development standards.
In conclusion, for an IDP to succeed, it must be both scalable and flexible. Scalability guarantees that your platform can grow with your organization, while flexibility ensures it can adapt to the unique demands of diverse projects and development teams. Together, these characteristics lay the technical groundwork for a highly effective Internal Developer Platform.
#Tip 2: Automate Routine Maintenance Tasks
Automation is the cornerstone of efficient IDP management. Organizations can automate routine maintenance tasks to save time and reduce the potential for human error.
#The Value of Automation
From a technical standpoint, automation refers to using scripts, tools, or processes to perform routine tasks with minimal human intervention. In the context of IDPs, automation plays a crucial role in streamlining maintenance activities, saving time, reducing errors, and ensuring consistency across the platform.
Examples of Automated Tasks:
- Environment Provisioning and Cleanup: When developers create new environments for their projects, whether for development or testing, automating the provisioning and deprovisioning processes can be highly beneficial. Tools like Terraform and AWS CloudFormation enable you to define your environment's infrastructure as code. Tools like Qovery enable ephemeral environments for each pull request and automatically shut down once merged. This means you can automatically spin up and tear down environments with a single command. In this way, you save time and ensure that every environment is consistent and compliant with your defined infrastructure.
- Backup and Restore: Regularly backing up IDP data and configurations is essential for disaster recovery. With automation, you can schedule automated backups and easily restore the platform to a previous state if issues arise. For example, automation tools like Ansible can script these backup and restore processes, ensuring they occur at the appropriate intervals without manual intervention.
- Security Patching: Keeping your IDP and its underlying infrastructure up to date with the latest security patches is a critical task. However, it can be time-consuming and error-prone if done manually. Automation frameworks like Chef or Puppet can automate the deployment of security patches across your IDP. This reduces the risk of vulnerabilities and ensures that updates are consistently applied.
- Resource Scaling: As your organization grows, your IDP may need to scale with it. Automation can take care of this process. Tools like Kubernetes autoscaling can automatically add or remove resources based on predefined criteria, such as CPU utilization or incoming request volume. This ensures that your IDP can handle increased loads without manual intervention.
#Automation Challenges and Considerations
While automation offers immense benefits, it's not without its challenges:
- Initial Setup: Implementing automation requires an initial time and resource investment. You need to create scripts or configure automation tools. However, this upfront effort pays off in the long run.
- Monitoring and Oversight: Automated processes still need oversight. Regularly monitor the automation to ensure it's working as intended. Alerts and notifications can notify you of any issues.
- Security: Ensure that your automated processes are secure. Automation scripts and tools can become potential attack vectors, so it's crucial to follow best practices for securing your automation solutions.
Automation is a technical cornerstone of effective IDP management. By automating routine maintenance tasks, you can increase efficiency, reduce the risk of human error, and maintain the consistency of your IDP. Whether it's provisioning environments, performing backups, applying security patches, or scaling resources, automation is a fundamental practice for a well-managed Internal Developer Platform.
#Tip 3: Implement Monitoring and Analytics
The technical side of implementing monitoring and analytics is vital for keeping IDPs in good health. Monitoring is not just about tracking system performance; it's about gathering data that can drive informed decisions. Let’s delve into the key technical aspects of this crucial practice and how it plays a pivotal role in IDP efficiency and performance.

#The Role of Monitoring and Analytics
For technical teams overseeing an IDP, monitoring and analytics serve as the eyes and ears of the platform. These practices provide a real-time view of its performance, stability, and user experience. Additionally, they offer historical data that aids in troubleshooting, optimization, and decision-making.
Here are the technical facets to consider:
- Key Performance Metrics: Begin by defining and monitoring key performance indicators (KPIs) relevant to your IDP. These could encompass metrics like response times, resource utilization, environment provisioning speed, and error rates. It's imperative to establish benchmarks and alert thresholds to detect and address issues promptly.
- Data Collection and Storage: To effectively monitor your IDP, you need to collect data. The platform should be equipped with mechanisms to log and store information about activities, user interactions, resource utilization, and more. Tools such as the Elastic Stack (Elasticsearch, Logstash, and Kibana) can assist in aggregating, visualizing, and analyzing this data.
- Real-Time Alerting: Technical teams need to be alerted when anomalies or issues arise. Implement real-time alerting systems that notify administrators, DevOps, or IT teams when predefined thresholds are exceeded. Platforms like Prometheus and Grafana are popular choices for this purpose.
- Security and Compliance Monitoring: Security is a primary concern when managing an IDP. Incorporate security monitoring into your platform to detect and respond to suspicious activities or breaches. Ensure that security logs and audit trails are generated and monitored continuously to align with industry compliance standards.
#Tools and Technologies
Several tools and technologies are instrumental in implementing monitoring and analytics for an IDP:
- Prometheus: An open-source monitoring and alerting toolkit designed for reliability and scalability. It can gather metrics from various systems and store them for analysis.
- Grafana: A popular open-source platform for creating and sharing interactive dashboards. It integrates well with Prometheus and other data sources, providing powerful visualization capabilities.
- Elastic Stack: Comprising Elasticsearch, Logstash, and Kibana, this stack is widely used for log and data analytics. Elasticsearch stores and indexes data, Logstash processes it, and Kibana offers a user-friendly interface for visualization.
- Security Information and Event Management (SIEM) Solutions: SIEM solutions like Splunk and the ELK Stack (Elasticsearch, Logstash, and Kibana) are crucial for security monitoring. They provide real-time analysis of security alerts generated by applications and network hardware.
#Challenges and Considerations
Monitoring and analytics may present challenges that need to be addressed:
- Data Overload: It's easy to drown in data. Ensure that you collect and analyze only the most relevant data, or you risk overwhelming your teams and tools.
- Alert Fatigue: Poorly configured alerting systems can lead to alert fatigue. Configure alerts carefully and fine-tune thresholds to avoid unnecessary distractions.
- Data Security: The data collected during monitoring may include sensitive information. Ensure robust data security practices are in place to protect this data from unauthorized access or breaches.
Monitoring and analytics are the technical bedrock of IDP management. By actively monitoring key metrics, collecting relevant data, and implementing alerting systems, your team ensures the IDP's stability, performance, and security. This data-driven approach is essential for maintaining a well-managed Internal Developer Platform.
#Tip 4: Ensure Security and Compliance
Incorporating robust security and compliance measures within IDPs is paramount. Security is not just a checklist; it's a continuous process that should be deeply integrated into the IDP. Let’s delve into the technical considerations and best practices for ensuring the security and compliance of your Internal Developer Platform (IDP).
#Technical Aspects of Security and Compliance
- Access Controls: Implement robust access controls to ensure that only authorized personnel can access the IDP. This includes role-based access, user authentication, and permissions management. Technical controls should be in place to enforce access restrictions. For example, Identity and Access Management (IAM) systems, such as AWS Identity and Access Management, can help manage access to AWS resources.
- Data Encryption: Ensure that data at rest and in transit is encrypted. This safeguards sensitive information from unauthorized access. Tools like Transport Layer Security (TLS) and File and Disk Encryption mechanisms should be in place to encrypt data both in transit and at rest.
- Audit Trails: Generate detailed audit trails that record actions taken within the IDP. These logs serve as a technical record of events and activities for compliance and security auditing. Security Information and Event Management (SIEM) systems like Splunk, ELK Stack, or specialized audit trail tools can be used to collect and analyze these logs.
- Penetration Testing and Vulnerability Scanning: Regularly perform penetration testing and vulnerability scanning on your IDP. This involves simulating cyberattacks to identify vulnerabilities and weaknesses in your system. Tools like OWASP ZAP and Nessus can be used for this purpose.
- Compliance with Industry Standards: Depending on your industry, there may be specific compliance standards that your organization must adhere to, such as HIPAA, GDPR, or SOC 2. Ensure that your IDP is configured to meet these standards. For instance, GDPR compliance would involve data protection and privacy measures, while HIPAA compliance would entail strict security and privacy controls for healthcare data.
#Examples of Security Measures
- Multi-Factor Authentication (MFA): Implement MFA to add an additional layer of security. Users must provide two or more verification factors to access the IDP. This commonly involves something the user knows (password), something the user has (smartphone), and something the user is (fingerprint or face scan).
- Data Masking: In situations where sensitive data must be displayed to users, consider data masking. This technique conceals certain characters in sensitive data to protect it from unauthorized access. Databases often have built-in data masking features.
- Regular Security Patching: Keep your IDP and its components up to date with security patches. Vulnerabilities in software can be exploited by attackers, so timely patching is crucial.
- Role-Based Access Control (RBAC): Implement RBAC to define the actions that different roles can perform within the IDP. For instance, developers might have different access rights compared to administrators.
#Challenges and Considerations
- Balancing Security and Usability: Security measures should enhance security without impeding usability. Striking this balance is a challenge, but it's essential for user acceptance.
- Compliance Complexity: Achieving and maintaining compliance with industry standards can be complex. It often requires ongoing effort, documentation, and adherence to specific practices.
- Data Protection: IDPs often handle large volumes of data. Ensuring data protection through encryption and access controls can be technically demanding.
The security and compliance of an IDP are deeply technical endeavors. Implementing strong access controls, data encryption, audit trails, and compliance measures is essential. These security practices safeguard the IDP's data and operations and help build trust with users and stakeholders.
#Tip 5: Foster Collaboration and Training
Creating a culture of collaboration and providing technical training are essential to optimize IDP usage. Let’s dive into the technical aspects of promoting collaboration among development teams through your Internal Developer Platform (IDP). It also highlights the importance of technical training for ensuring teams can effectively use the IDP.
#Technical Benefits of Collaboration
- Cross-Functional Integration: An IDP can be technically configured to bring different teams and roles into the same development process. For example, integrating development, quality assurance, and operations teams within the IDP creates a seamless workflow. This involves setting up permissions, access controls, and pipelines to facilitate cross-functional collaboration.
- Real-time Collaboration: Many modern IDPs support real-time collaboration features. Technical implementations of features like live code collaboration, instant messaging, or video conferencing can be integrated into the platform to enable instant communication and joint problem-solving.
- Workflow Automation: Collaborative workflows can be technically optimized for efficiency through workflow automation. For instance, automating the movement of code from development to testing, to staging, and eventually to production streamlines processes. Workflow automation tools, often integrated into the IDP, can include Jenkins, GitLab CI/CD, or similar solutions.
- Feedback Loops: Technical setups for feedback loops within the IDP allow for quicker issue resolution and process improvement. Automated reporting, issue tracking, and notifications can be integrated to create technical feedback mechanisms.
- Shared Environments: From a technical perspective, setting up shared development and testing environments is key to collaboration. Shared environments enable different teams to access the same application or system, allowing them to coordinate and provide input effectively.
#Technical Aspects of Training
- Onboarding Workflows: Implement technical onboarding workflows within the IDP to guide new team members through the platform's features and best practices. This could include a series of interactive tutorials or guided setup processes.
- Interactive Documentation: Develop interactive documentation within the IDP. This can include clickable demos, code samples, and hands-on exercises to help users understand the platform. Tools like Swagger can be used to create interactive API documentation.
- Certification Paths: Technical training programs can include certification paths for various roles within the IDP. For example, a DevOps engineer might have a certification path that covers automation, deployment, and security within the IDP.
- User Support Channels: Provide technical support channels for IDP users. This could include chat support, forums, or ticketing systems. These channels should have a technical support structure to address user issues effectively.
#Challenges and Considerations
- User Adoption: Encouraging users to collaborate within the IDP can be challenging. Ensure the technical setup is intuitive and user-friendly.
- Security: Collaborative tools must be secured to protect sensitive data. This involves technical measures like encryption and access controls.
- Scaling Collaboration: As your organization grows, scaling collaborative features and training becomes more complex. Plan for scalability in your technical setup.
Fostering collaboration and providing technical training within the IDP are critical components of effective IDP management. These technical efforts enable teams to work together seamlessly and empower them to make the most of the platform. Collaboration tools, interactive training, and support channels should be tailored to your organization's specific needs and goals.
#Conclusion
The above tips, ranging from scalability and automation to monitoring and collaboration, provide a robust foundation for managing your IDP. They're a testament to the technical complexity that IDPs involve. But more than that, they're a testament to the infinite potential for improvement in software development. Consider these tips not as a static list of recommendations but as a dynamic roadmap for your journey in IDP management. By applying them to your specific context and continuously seeking technical excellence, you'll unlock greater efficiency, security, and collaboration in your software development processes.
The challenges of IDP management may be formidable, but so are the rewards. Faster development cycles, enhanced software quality, and more cohesive teams await those who embrace these tips with technical acumen. Whether you're an experienced DevOps engineer or a budding software developer, these insights can help you navigate the complexities of IDPs.
Your Favorite DevOps Automation Platform
Qovery is a DevOps Automation Platform Helping 200+ Organizations To Ship Faster and Eliminate DevOps Hiring Needs
Try it out now!

Your Favorite DevOps Automation Platform
Qovery is a DevOps Automation Platform Helping 200+ Organizations To Ship Faster and Eliminate DevOps Hiring Needs
Try it out now!